It has been a huge week for acquisitions in tech, with announcements of definitive agreements for Tech Data Corp. to go private, Mirantis to pick up Docker's Enterprise Platform business and OpenText to buy Carbonite Inc.
The deal impacting the most channel companies is Tech Data. Loosely speaking, Apollo Global Management Inc. is buying Tech Data for $5.4 billion, a 24.5 percent premium to Tech Data's share price as of mid-October. Technically, the acquisition is being engineered by "an affiliate of funds managed by affiliates of Apollo."
Rumors have been widespread about a coming acquisition for the distribution giant, as acknowledged in the news release Wednesday about the deal, which declared Oct. 15 as "the last trading day prior to published market speculation regarding a potential transaction involving the company."
Assuming no better offers come forward in the go-shop period through Dec. 9, and that the agreement passes regulatory muster, the deal is expected to close in the first half of 2020.
Existing channel partners can probably expect little to change in the short term. Tech Data CEO Rich Hume would stay on and company headquarters would remain in Clearwater, Fla. Executives from Tech Data and Apollo both affirmed the commitment to Tech Data partners and to the business in general. They positioned the deal as a way for Tech Data, free of quarterly financial reporting pressures, to focus on long-term growth.
Docker-Mirantis
Container technology pioneer Docker Inc. is selling a part of its business to Mirantis for an undisclosed amount. The deal, also announced Wednesday, involves the Docker Enterprise Platform business, employees and enterprise customers.
Mirantis, known for its Kubernetes K8s-as-a-service, will get the Docker Enterprise Platform technology, including Docker Enterprise Engine, Docker Trusted Registry, Docker Unified Control Plane and the Docker CLI.
In a blog post, Mirantis CEO and co-founder Adrian Ionel said Mirantis will be able to enhance the Docker technologies with its K8s-as-a-Service technology. However, the move leaves out the Docker Swarm container orchestration technology.
Mirantis "currently expects to support Swarm for at least two years, depending on customer input into the roadmap," Ionel said. "Mirantis is also evaluating options for making the transition to Kubernetes easier for Swarm users."
As a company, Docker will now focus on Docker Desktop and Docker Hub.
OpenText-Carbonite
Earlier in the week, OpenText on announced an agreement to acquire Carbonite Inc. for $1.42 billion in another deal that had been reported publicly as being in the works. The deal amounts to a 78 percent premium on Carbonite's "unaffected closing stock price on September 5, 2019, the last trading day before a media report was published speculating about a potential sale process," the companies said in a statement.
Carbonite specializes in data protection and security, while OpenText is focused on enterprise information management.
OpenText CEO & CTO Mark J. Barrenechea positioned the pending acquisition as strengthening OpenText in cloud platforms and giving the company new routes to markets via Carbonite's "SMB/prosumer channel and products."
The companies expect the transaction to close within 90 days.
Posted by Scott Bekker on November 14, 20190 comments
There was a gigantic deal in the managed service provider (MSP) tools market this week that changes, well, not that much in the short run.
ConnectWise is acquiring Continuum. Both are major players in the MSP market. ConnectWise has a long legacy in the professional services automation end of the space, which it has been increasingly building into a full-stack MSP solution that includes remote monitoring and management (RMM), quote tools and various other business and technology pieces. Continuum is a younger company, born out of a partial Zenith Infotech acquisition, that focused heavily on providing turnkey MSP technology tools and operations center-provided services to MSPs with fewer technicians on staff.
Both have large bases of MSP customers/partners, making the deal important in terms of the number of partners affected.
Yet, there is more that doesn't change, at least immediately, from this deal than does.
For one thing, both companies are already owned by Thoma Bravo, the private equity behemoth that's been funding much of the M&A activity in the MSP sector. The Thoma Bravo portfolio also includes SolarWinds and Barracuda Networks. Interestingly, ConnectWise was acquired by Thoma Bravo in February and at the time denied rumors that an acquisition was pending for another Thoma Bravo company.
ConnectWise also says it remains committed to keeping its platform open to competitors, so that MSPs can choose on their own best-of-breed combinations of tools. "We believe in an open ecosystem, the power of choice and providing a single pane of glass view," the company said in its statement Wednesday announcing the deal. The announcement came during IT Nation 2019, ConnectWise's annual partner conference, which features more than 100 exhibitors, including direct competitors in several areas. Many of those vendors must keep a close eye on whether that commitment to openness continues, but for now ConnectWise is saying the right things.
The most significant part of the announcement is that the company intends to continue offering both RMMs, meaning little change for existing partners. In the announcement, which also covered the acquisition of ITBoost and a partnership with Webinfinity, ConnectWise emphasized how all the pieces fit together.
"The resulting solution suite redefines business automation. The convergence of ConnectWise's best-in-class platform (PSA, RMM, CPQ), with the service-enabled RMM, security and NOC/SOC and Help Desk from Continuum, IT documentation from ITBoost, and partner relationship management (PRM) from Webinfinity, substantially increases value to [technology service providers]. ConnectWise becomes the only software platform that connects the TSP upstream to its suppliers and downstream to its customers, creating a unified business operating environment to accelerate TSPs success," the statement said.
Specifically about any potential overlap between the ConnectWise/Continuum tools, ConnectWise positioned the RMM approaches as complementary.
Describing the Continuum tools and services, ConnectWise positioned Continuum's model as appropriate for TSPs "preferring to outsource much of their low-level work, whether because they want additional help on nights or weekends, or because they need to access a different skillset than they possess. This complements ConnectWise's current offering, which targets TSPs who take more of a 'do it yourself' approach. As a result, TSPs will have the freedom to adopt either model, or a mixture of both, all while making more data driven decisions and increasing their use of automation."
Competitors are going through the motions of seeding doubts for ConnectWise or Continuum MSPs about potential de-emphasis of their preferred tools in the future.
"Some hiccups are, of course, to be expected for a deal of this size," said Kaseya CEO Fred Voccola in a statement. "For example, both ConnectWise and Continuum are relatively the same size and offer users competing RMMs. And while they, in theory, could continue maintaining two RMMs simultaneously, they'll likely focus instead on investing in just one tool's continued R&D, technical support and customer enablement. This will ultimately force half of its users to migrate to the company's preferred tool -- an often costly and time-consuming effort."
Datto's CTO Bob Petrocelli was less direct, but addressed big questions for MSPs to keep in mind after a merger in a blog that was posted after the merger but that didn't mention ConnectWise or Continuum specifically.
"There are steps you can take to anticipate how consolidation among vendors may affect your business as an MSP. Look for transparent communication from your vendor. Why did they make this decision? How does the tech benefit you? How will your partnership change and improve? These are a few good questions your vendor should provide answers to," Petrocelli wrote.
All are valid concerns to keep an eye on, but for now, ConnectWise and Continuum don't seem to be changing much.
Posted by Scott Bekker on October 31, 20190 comments
The conventional wisdom was that the massive Joint Enterprise Defense Infrastructure (JEDI) contract was Amazon Web Services' to lose.
Then Microsoft was named on Friday as the winner of the contract to be the sole cloud contractor for the Pentagon -- a deal valued at up to $10 billion over 10 years if all the options are exercised.
Here's how Adam Mazmanian at Federal Computer Week described what it means for Microsoft in a comprehensive piece on the deal:
The market agreed on Monday morning, with TheStreet reporting:
Victory laps by Microsoft could be premature, however.
Kara Swisher, the New York Times columnist and CNBC contributor who has some of the best sources in Silicon Valley, warned everyone not to expect AWS to take the decision as final. Especially given President Donald Trump's public statements about Amazon CEO Jeff Bezos.
In an appearance Monday on CNBC, Swisher said:
Some of the Trump rumors come from former Defense Secretary James Mattis. Here's a CNBC report on a portion of Mattis' book:
Of Microsoft, Swisher said:
Amazon's public statements so far, out of a spokesperson, are that the company was "surprised" by the decision. No word yet on whether it'll decide to tie it up in litigation or focus on winning some of the many other cloud service deals that are expected to come out of the U.S. federal government over the next few years.
This decision is a big win for Microsoft. As for the challenge aspect, think of it like the replay rule in the NFL. The refs have to overturn the ruling on the field, and the ruling on the field is that the JEDI contract belongs to Microsoft. But as the decision Friday showed, anything can happen, and may yet.
Posted by Scott Bekker on October 28, 20190 comments
Microsoft's Internet of Things (IoT) platform for solution-building partners, known as Azure IoT Central, is being overhauled with a number of major feature updates intended primarily for OEMs, independent software vendors (ISVs) and systems integrators (SIs).
The company released details of the IoT Central changes on Monday as part of a raft of IoT announcements timed to coincide with the IoT Solutions World Congress taking place this week in Barcelona.
Azure IoT Central Features
Microsoft describes IoT Central as an app platform that provides partners with IoT plumbing for connecting devices, managing devices and performance analysis. Partners take their own business and vertical expertise to build an IoT solution on top of the Microsoft framework. They can then white-label the Microsoft parts under their own solutions and either sell directly to customers or sell through the Microsoft AppSource marketplace.
"The value of IoT Central is brought to life when solution builders leverage it to connect and manage their devices, as well as to extend device insights into their line of business applications. This allows solution builders to spend their time and energy in their area of expertise, transforming their businesses through value-adding and brand-differentiating elements," explained Bert Van Hoof, partner group program manager for Azure IoT, in a blog post describing the new features. The blog post provided one of the clearest explanations yet of Microsoft's partner intentions for IoT Central.
Along that theme, several of the coming enhancements address the particular concerns of partners, who need infrastructure that enables them to handle several customers at once and who benefit the most from aspects of Microsoft solutions that allow for repeatable procedures.
One is multitenancy, the ability to have several customers whose individual tenants are separated from one another for security purposes but that can be managed collectively by one partner. "We know that many solution builders need more than just repeatability; they also need manageability to truly scale their investments to customers. Which is why in the coming months, Azure IoT Central will support multitenancy; solution builders can build once and use a multitenancy interface to on-board, configure, and update many customers and organizations globally across regions, offering both device and data sovereignty without sacrificing manageability," Van Hoof said.
Another is public APIs to access features. "Solution builders with extensibility needs beyond device data now have access to Central features through our public APIs. Users can develop robust IoT solutions that leverage IoT Central programmatically as the core for device modelling, provisioning, lifecycle management, operations (updating and commanding), and data querying," he said.
In an effort to jump-start partner practices, Microsoft is also immediately releasing 11 new industry app templates, which are designed to illustrate the types of solutions that partners and customers can build. For retail partners, the templates include Store Analytics Condition Monitoring, Store Analytics Checkout, Digital Distribution Center, Connected Logistics and Smart Inventory Management. For government partners, the templates are Water Quality Monitoring, Water Consumption Monitoring and Connected Waste Management. Microsoft is also providing energy vertical templates of Smart Meter Monitoring and Solar Power Monitoring, and a health care template for Continuous Patient Monitoring.
Other new features for IoT Central include support for IoT Edge, support for IoT plug-and-play, the ability to save and load applications, new data export options, and custom user roles. Microsoft will also roll out a new pricing model sometime next year that is supposed to make the solution's cost more predictable.
Azure Sphere GA Date
Also Monday, Microsoft set a February 2020 general availability date for Azure Sphere. Azure Sphere is Microsoft's ambitious initiative, first announced in April 2018, to put itself at the center of IoT management and security. It consists of a combination of a reference architecture for microcontroller units (MCUs), a Linux-based operating system for the devices themselves, and a cloud-based Azure Sphere Security Service to manage and secure the devices. Earlier this year, Microsoft added a mechanism called "Guardian Modules" to the roadmap, which would serve as a bridge for older IoT devices to be managed under Azure Sphere.
Sam George, corporate vice president of Azure IoT, in a blog post highlighted momentum with the preview versions of Azure Sphere. "Since we first introduced Azure Sphere, we've made tremendous progress delivering on our ambitious product vision, investing in partnerships and capabilities that help us serve customers wherever they are in their IoT journey. This includes our partnerships with silicon leaders to enable heterogeneity at the edge; our longstanding partnership with MediaTek, and our recent partnership announcements with NXP and Qualcomm, which will introduce the first cellular-enabled Azure Sphere-certified chip," George wrote.
Other IoT Enhancements
Microsoft disclosed several other coming enhancements on Monday.
Several new features will reach general availability by the end of November for Azure IoT Hub, the cloud gateway used by IoT Central. The runtime of the Azure Event Grid will be extended to devices with Azure Event Grid on IoT Edge, which allows organizations to publish their own events or connect other modules with built-in event capabilities. Organizations will be able to put their own information into messages with IoT Hub message enrichment. Additionally, IoT Hub will integrate with the regular Azure Event Grid for sending device telemetry events to Azure services.
Azure Maps is already a feature with a lot of usage scenarios for IoT applications that include devices in the field. Now Microsoft is partnering with AccuWeather to add geospatial weather intelligence data into those applications. Common scenarios include "routing, targeted marketing and operations optimization," George said.
Finally, Microsoft is working on a handful of new capabilities for Azure Time Series Insights, which is Microsoft's IoT analytics solution. Those include multilayered storage, flexible cold storage, richer analytic capabilities, scale and performance improvements, and a Power BI connector.
Posted by Scott Bekker on October 28, 20190 comments
Of Microsoft's three main business units, Intelligent Cloud accounted for slightly less revenue than either of the other two units, but still generated some of the most interesting activity this quarter.
Microsoft on Wednesday reported results for the first quarter (July-September) of its fiscal 2020. The company beat Wall Street expectations on both earnings and revenues, although the stock barely moved. Compared to the year-ago quarter, revenues were up 14% to $33 billion and earnings per share were up 21% to $1.38.
Microsoft's three business units all brought in roughly similar amounts of revenue for the quarter. More Personal Computing saw revenues of $11.1 billion, Productivity and Business Processes also had $11.1 billion, and Intelligent Cloud was $10.8 billion.
By revenue growth, Productivity and Business Processes, which includes Office, LinkedIn and Dynamics, was closest to the top-line growth revenue percentage at 13%. Intelligent Cloud, which includes Azure, server products and services, grew revenue at about twice the rate of the rest of the company -- 27%. More Personal Computing lagged the company's overall revenue growth, with a 4% increase.
In his prepared statement for the earnings release, CEO Satya Nadella highlighted Intelligent Cloud. "The world's leading companies are choosing our cloud to build their digital capability," Nadella said. He also pointed to the continuous rollout of more services and capabilities across Microsoft's cloud services stack.
Azure is the strategic tent pole of the division, and the results for Azure for the quarter were strong. Microsoft does not reveal Azure revenue figures, but the company details Azure growth rates every quarter.
While growth in Azure is slowing as the business gets larger, it remains robust and consistently compares favorably to segment leader Amazon Web Services' growth rates. Microsoft reported a 59% growth rate for Azure in Q1. A year ago that rate was 76%, and it has been slowly dropping in the interim quarters. For the record, Microsoft did say that Azure revenues grew at a 63% rate in the most recent quarter in constant currency.
In a positive note for Microsoft's unique hybrid cloud narrative, the server products, which include on-premises systems, had a surprising surge in the quarter. A year ago, server products grew at a 10 percent rate and had fallen to 5% growth in Q4 of 2019. Yet in Q1 2020, server products were up 12%. Microsoft attributed some of the growth to demand related to SQL Server 2008 and Windows Server 2008 end of support.
Other notable highlights in the quarterly results included:
- Revenues for the Microsoft Surface line of 2-in-1s and laptops dropped 4%.
- Dynamics 365 had a strong quarter with revenue growth of 41%.
- Office 365 Commercial revenue shot up 25%.
- Windows OEM revenue was up 9% as the January 2020 support deadline for Windows 7 approaches.
- LinkedIn revenue was up 25%.
- Enterprise Services revenue was up 7%.
- The Xbox unit was flat.
Posted by Scott Bekker on October 23, 20190 comments
SherWeb is urging its partners to go after the managed security services opportunity aggressively in 2020.
The Sherbrooke, Quebec-based cloud distributor, one of the indirect providers in Microsoft's Cloud Solution Provider (CSP) program, held its annual partner conference late last week in Montreal. SherWeb has thousands of partners who resell Microsoft and other cloud services through SherWeb as part of their primarily SMB-focused managed service provider (MSP) practices.
"We cannot emphasize enough how important and crucial security will be in our business," said Matthew Cassar, SherWeb's co-founder and co-CEO, in the main keynote at the SherWeb Accelerate Cloud Summit 2019.
"Managed service providers need to evolve into managed security service providers," Cassar said, adding that even MSPs who don't shift gears to security should at least offer holistic security as part of their services. According to SherWeb market research, about 90 percent of SMBs would switch service providers if they were provided a comprehensive security service.
Cassar and other SherWeb executives detailed several ways that they plan to help their MSP partners offer more effective security services to SMB customers, who are finding themselves targeted by attackers more frequently than they used to be when hacks focused more heavily on large multinationals.
For one thing, Cassar said SherWeb will be offering best-of-breed third-party security services that its partners can in turn offer to their customers. As a first component, SherWeb announced at the show that it is offering Bitdefender Antivirus.
"Bitdefender Antivirus is a key security product for any MSP to resell because it will help them detect threats more accurately than any other security product on the market," said Nicolas Roy, product manager for security at SherWeb, in a statement. "As part of our commitment to provide our partners with only the best business software in the world, we're proud to add Bitdefender to our portfolio."
A little further out, Cassar said SherWeb will be providing security operations center (SOC) services for its partners in the coming months.
Another way SherWeb plans to help its partners expand their security capabilities is by enhancing Office Protect, the company's simplicity-focused solution for locking down Office 365 deployments. The company first launched Office Protect at its 2018 conference, and the core purpose of the product remains intact, said Guillaume Boisvert, director of Office Protect for SherWeb. "We know that our value, our positioning is to be simple, to make it easy," Boisvert said. "A lot of security products, if I can send a million alerts, you can see that I'm useful. That is definitely not our approach."
Improvements for Office Protect on the roadmap include advanced reporting to cover compliance workloads. Additionally, plans call for Office Protect to handle more investigation and remediation of potential security incidents. "I don't want to tell you that we'll do the remediation for you. That's just a pipe dream," Boisvert said. "We're not looking to take the decision away from you. We're looking to accompany you through the investigation. We're going to provide you with the playbooks. [For example,] it's a sign-in from an unauthorized country. I got an alert in clear English. What's next?"
That is the type of issue for which Office Protect will recommend to the partner how to handle the customer's situation, he said.
In non-security developments, SherWeb announced that it will offer QuickBooks for its partners to resell. "This has been a high-demand product from our partners," Cassar said. Additionally, Cassar said that over the last year, existing partners had increased their subscription-based revenues by 30 percent and increased their average revenue per user (ARPU) by more than a third to $15.
Posted by Scott Bekker on October 15, 20190 comments
The SherWeb Accelerate Cloud Summit kicks off this week in Montreal, where it will provide its annual window into the opportunities and challenges facing smaller, Microsoft-focused managed service providers (MSPs).
SherWeb is one of the handful of indirect providers in Microsoft's Cloud Solution Provider (CSP) program, meaning SherWeb obtains Office 365 and other subscriptions from Microsoft and distributes those subscriptions, along with other services and support, to a large network of smaller CSP partners who work directly with their own customers.
"We're trying to help our partners grow, diversify and survive in this new evolution of cloud services," said Marc-André Fontaine, vice president of sales and marketing at SherWeb, in an interview about the conference, which runs from Wednesday through Friday. It's the third year for the conference, and the second year in Montreal, which is not far from SherWeb's headquarters in Sherbrooke, Quebec.
"If you look at the demographic of the conference, it's really meant for partners who do not have dedicated sales and marketing people," Fontaine said.
The three major themes this year will reflect those partners' needs, Fontaine said. One is sales and marketing, the second is helping MSPs become more security-oriented and the third is on diversifying beyond just Office 365 sales.
While all three themes will be present in SherWeb Co-founder and CEO Matthew Cassar's kickoff keynote, sales and marketing will be front and center in sessions on building cloud-service bundles, using LinkedIn to drive leads, and accelerating and optimizing customer acquisition strategies.
Security is the theme of the final day's keynote, when high-profile former hacker Michael "Mafiaboy" Calce talks about cybercrime trends. Several of the more technical pre-show sessions on Wednesday also focus on securing Office 365, overall cyber protection, improving governance in Microsoft Teams, and layered protection and response.
Diversification of revenue streams is part of the security theme, but SherWeb also plans sessions around opportunities in voice-over-IP (VoIP), Dynamics 365 for Sales Professionals, Azure and infrastructure-as-a-service (IaaS).
One partner returning to the SherWeb conference, Reza Palizban, says he's looking forward to the sales and marketing sessions, as well as SherWeb product and service roadmap details.
For Palizban, president and co-founder of Aegis Innovators in San Diego, the SherWeb show was the right content at the right time. "It was the best conference I went to in 2018. There were a couple hundred partners in a room with high-quality educational speakers talking about key components of marketing your business -- what to say, what not to say. Every minute I was listening and dialed in, it was really, really good," he said.
Posted by Scott Bekker on October 08, 20190 comments
We're on a slight detour in the steady drive by hyperscale service providers toward ever more compute, storage and networking gear in their datacenters.
The hyperscale service providers are companies like Amazon Web Services (AWS), Microsoft and Alphabet, which each are building and expanding dozens of datacenters worldwide to provide public cloud services to business and government customers.
As those companies and a few other huge competitors have physically positioned themselves to dominate the public cloud service market, their massive purchases have become an increasingly large portion of overall IT infrastructure spending.
IDC this week released figures for the second quarter of 2019 (April-June), showing a decline of 15 percent compared to the year-ago quarter in vendor revenue from hardware infrastructure sales to public cloud environments. The revenue total was $9.4 billion for the quarter.
As the Framingham, Mass.-based research company's statement put it: "This segment of the market continues to be highly impacted by demand from a handful of hyperscale service providers, whose spending on IT infrastructure tends to have visible up and down swings."
In all, sales of IT infrastructure products for cloud environments dropped by 10 percent quarter-over-quarter, when including private cloud spending, which also decreased but at a less severe pace of about 1 percent.
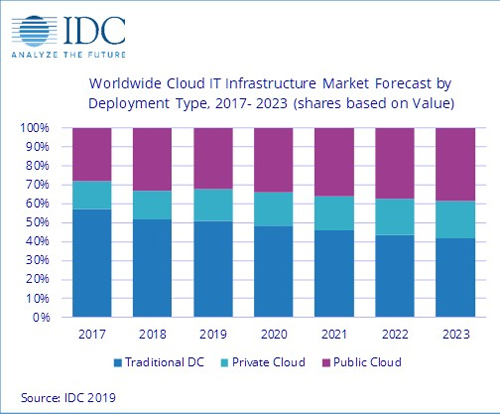 IDC sees cloud IT infrastructure sustainably overtaking traditional datacenter spending in 2020. (Source: IDC)
IDC sees cloud IT infrastructure sustainably overtaking traditional datacenter spending in 2020. (Source: IDC)
The market researchers had anticipated declines this year after a free-spending 2018. In the first-quarter report back in June, IDC's Natalya Yezhkova cautioned against reading too much into the expected drop-off.
"As the overall IT infrastructure goes through a period of slowdown after an outstanding 2018, the important trends might look somewhat distorted in the short term," Yezhkova, research vice president of Infrastructure Systems, Platforms and Technologies at IDC, said in a statement. "IDC's long-term expectations strongly back continuous growth of cloud IT infrastructure environments. With vendors and service providers finding new ways of delivering cloud services, including from IT infrastructure deployed at customer premises, end users have fewer obstacles and pain points in adopting cloud/services-based IT."
With its September update, which includes Q2 results, IDC is now calling for the public cloud IT infrastructure segment to drop by nearly 7 percent from 2018 to about $42 billion in vendor revenues for all of 2019.
The pullback in spending is delaying the crossover point when more money will be spent on cloud infrastructure (both public cloud and private cloud) than on traditional IT environments. While cloud IT infrastructure spending was already briefly higher than traditional IT infrastructure spending in the third quarter of 2018, IDC now forecasts that for the full year of 2019, slightly more money will be spent on traditional IT infrastructure than cloud IT infrastructure. As for the public/private cloud mix, about two-thirds of cloud IT infrastructure spending comes from the hyperscale, public cloud providers.
This detour aside, IDC anticipates steady growth in spending on cloud IT infrastructure in 2020 and beyond -- leading to the cloud side outpacing the traditional side in revenues on a sustained basis.
Posted by Scott Bekker on September 26, 20190 comments
It's always interesting when Microsoft acknowledges the use of a major third-party product for internal purposes. Microsoft has always tried to offer it all when it comes to software and services -- or at least as much of it as possible.
But later this month, the company will be pulling back the curtain on how it uses Red Hat Ansible Automation in its Fortune 100-class operations. Microsoft will be one of several Red Hat customers speaking at AnsibleFest Atlanta from Sept. 24 to 26. Other customers talking about their Ansible adoption at the show include Datacom, Energy Market Company and Surescripts.
Launched in 2013, Red Hat Ansible Automation is a tool for automation across the stack from infrastructure to networks to cloud to security for both IT operations and development.
"Adopting Red Hat Ansible Automation has not only changed how our networks are managed, but also sparked a cultural transformation within our organization," said Bart Dworak, Microsoft's software engineering manager for Network Infrastructure and Operations, in a statement. "By putting automation at the forefront of our strategy and not as an afterthought, we've been able to scale it in ways we did not know possible. Our engineers are now constantly looking for creative ways to solve their problems using Ansible Playbooks."
Microsoft turned to Ansible to improve the productivity of hundreds of engineers across 600 locations worldwide. Those engineers use Ansible for designing, building and deploying IT networks at scale, and the use of Ansible Automation has saved an estimated 3,000 work hours per year and reduced downtime.
For Microsoft, the Ansible deployment has a dogfooding element and AnsibleFest Atlanta will be an opportunity to drum up more partnership business with joint Red Hat-Microsoft customers. Microsoft's deployment of Red Hat Ansible Automation was done on top of Microsoft Azure.
Posted by Scott Bekker on September 16, 20190 comments
Longtime Microsoft senior executive and former Citrix president and CEO Kirill Tatarinov has been named executive vice chairman of Acronis, a provider of data protection solutions.
Tatarinov, who has been a member of the Acronis board for the last 10 months, will report to Founder and CEO Serguei Beloussov.
"Kirill will be an active member of the executive team, helping to accelerate Acronis' cyber strategy execution and scale the Acronis Cyber Platform and Acronis Cyber Infrastructure business. His experience with innovations at scale will help us to deliver easy, efficient and secure cyber protection to customers of any size," Beloussov said in a statement announcing Tatarinov's new role.
Tatarinov was president and CEO at Citrix for a year and a half from early 2016 to mid-2017. His tenure at Microsoft spanned 13 years and included stints as president of the Microsoft Business Solutions Division and corporate vice president of the Management and Solutions Division.
Posted by Scott Bekker on September 16, 20190 comments
In 2015, 6Wunderkinder CEO Christian Reber sold his company to Microsoft for an estimated $100 million to $200 million.
Now, the founder of the company that created the Wunderlist app has a new item on his public to-do list: convince Microsoft to sell the app back to him.
"Still sad @Microsoft wants to shut down @Wunderlist, even though people still love and use it. I'm serious @satyanadella @marcusash, please let me buy it back. Keep the team and focus on
@MicrosoftToDo, and no one will be angry for not shutting down @Wunderlist," Reber Tweeted last week to the official accounts of Microsoft CEO Satya Nadella and Marcus Ash, Microsoft's general manager for tasks in Berlin.
At the time of the June 2015 sale, the Berlin-based 6Wunderkinder claimed about 13 million users for the Wunderlist Pro and Wunderlist for Business software products.
Asked in a Twitter reply whether he was serious about proposing a business deal in a Tweet rather than through direct communication with Microsoft executives, Reber replied: "Serious offer."
As of Monday, original Tweet had 575 retweets and 2,400 likes.
The writing was on the wall for Wunderlist in April 2017, when Microsoft released a preview of a new Microsoft To-Do Office 365 application that was to eventually include Wunderlist capabilities. At the time, Microsoft indicated that its eventual aim was to retire the Wunderlist app.
It's unclear what Microsoft's actual timeframe is for discontinuing Wunderlist. In a Tweet (in German) last year after leaving Microsoft, Reber revealed that Microsoft was having technical difficulties porting Wunderlist's back end from Amazon Web Services (AWS) to Microsoft Azure.
In any event, Microsoft can now add a Twitter-based business offer to its list of tasks related to closing down Wunderlist.
Posted by Scott Bekker on September 09, 20190 comments
The VMware partnership with Microsoft to run VMware workloads natively on Microsoft Azure is coming to more datacenters over the next few months.
VMware CEO Pat Gelsinger provided a roadmap update for the partnership on Monday during his keynote at VMworld 2019 in San Francisco.
The formal name of the joint offering is Azure VMware Solutions. As described by Microsoft at the late-April unveiling, the agreement allows customers to run, manage and secure applications across VMware environments and Azure with a common operating framework. Supported VMware technologies include VMware vSphere, vSAN, NSX and vCenter.
At launch, the offering was available immediately in two Azure regions -- U.S East and U.S. West. (While partners often refer to Microsoft Azure "datacenters," Microsoft calls them Azure "regions," which the company defines as sets of datacenters "within a latency-defined perimeter and connected through a dedicated regional low-latency network.")
On Monday, Gelsinger said the offering is also available in a third Azure region, the West Europe region, with further global expansion coming soon. "By the end of the year, we'll be in Australia and Southeast Asia," Gelsinger said.
According to a graphic displayed behind Gelsinger, the footprint of the partnership will also broaden within some existing geographies before the end of this year. The offering should be up and running in Microsoft's Azure regions in Northern Europe, U.S, West 2 and South Central, which is also in the United States.
The graphic also showed that by the end of the first quarter of 2020, the offering will be added to Azure regions in Canada and Japan. That will bring availability of the VMware offering to 10 of Microsoft's 54 announced Azure regions.
The joint solution has attracted a few major customers. "Customers are already launching into this platform today. Over 20 customers are on it," said Gelsinger, naming Lucky Brands, Dot Foods and Gap.
Posted by Scott Bekker on August 26, 20190 comments